CVE-2019-15846: Unauthenticated Remote Command Execution Flaw Disclosed for Exim
CVE-2019-15846, a new unauthenticated remote code execution vulnerability in the Exim message transfer agent, has been patched in version 4.92.2. Users are encouraged to upgrade immediately.
Background
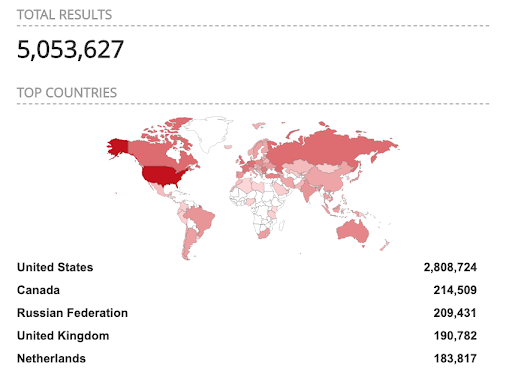
Exim Internet Mailer is a message transfer agent (MTA) for Unix hosts used to manage mail routing services for an organization. Exim is reportedly the most used MTA in the world, and has over 5 million internet-facing hosts, according to Shodan. Exploiting CVE-2019-15846 would allow a remote unauthenticated attacker to fully take control of a vulnerable Exim server.
Analysis
This vulnerability follows on the heels of CVE-2019-10149, another remote command execution (RCE) flaw which we blogged about in June. Exploitation attempts were seen one week later.
The Exim advisory describes CVE-2019-15846 as:
"The SMTP Delivery process in all versions up to and including Exim 4.92.1 has a Buffer Overflow. In the default runtime configuration, this is exploitable with crafted Server Name Indication (SNI) data during a TLS negotiation. In other configurations, it is exploitable with a crafted client TLS certificate."
As stated in the initial bug report by Zerons, an unauthenticated remote attacker could send a malicious SNI ending in a backslash-null sequence during the initial TLS handshake, which causes a buffer overflow in the SMTP delivery process. This would allow an attacker to inject malicious code that Exim then arbitrarily executes as root. This vulnerability does not depend on the TLS library in use, so both GnuTLS and OpenSSL are affected.
The default Exim configuration file does not have TLS enabled, but most organizations are required to enable it for standard internet traffic handling purposes. Some versions of Exim bundled with operating systems may have TLS enabled by default.
Proof of concept
A rudimentary proof-of-concept (PoC) exists, according to the Exim team, but has not been made public.
Solution
The Exim team has released version 4.92.2 to fix this vulnerability, and administrators are encouraged to upgrade as soon as possible. While the official security advisory notes that disabling TLS does mitigate the vulnerability, it is strongly recommended not to do so.
Identifying affected systems
As noted in Exim’s notification email: “We've indication that only versions starting with 4.80 up to and including 4.92.1 are affected.” It is also important to note that users running versions older than 4.80, while not vulnerable to CVE-2019-15846, are vulnerable to CVE-2018-6789, another critical RCE flaw. Additionally, the Exim project officially does not support versions prior to the current stable version, but does note in their advisory they will support package maintainers in backporting the fix where resources permit.
A list of Tenable plugins to identify this vulnerability can be found here.
Get more information
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface. Get a free 60-day trial of Tenable.io Vulnerability Management.
Learn more
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success