CVE-2019-15107: Exploit Modules Available for Remote Code Execution Vulnerability in Webmin

The popular Linux/UNIX systems management tool has more than 3 million downloads per year and the vulnerability has been present for at least a year, putting many virtual UNIX management systems at risk.
Background
On August 17, Webmin version 1.930 was released to address a remote code execution (RCE) vulnerability (CVE-2019-15107) present in Webmin versions 1.882 to 1.921. According to the Virtualmin site, “Webmin is the world's most popular Linux/UNIX systems management UI, with over three million downloads per year.” These vulnerabilities do have publicly available exploit modules, which puts many virtual UNIX management systems at risk.
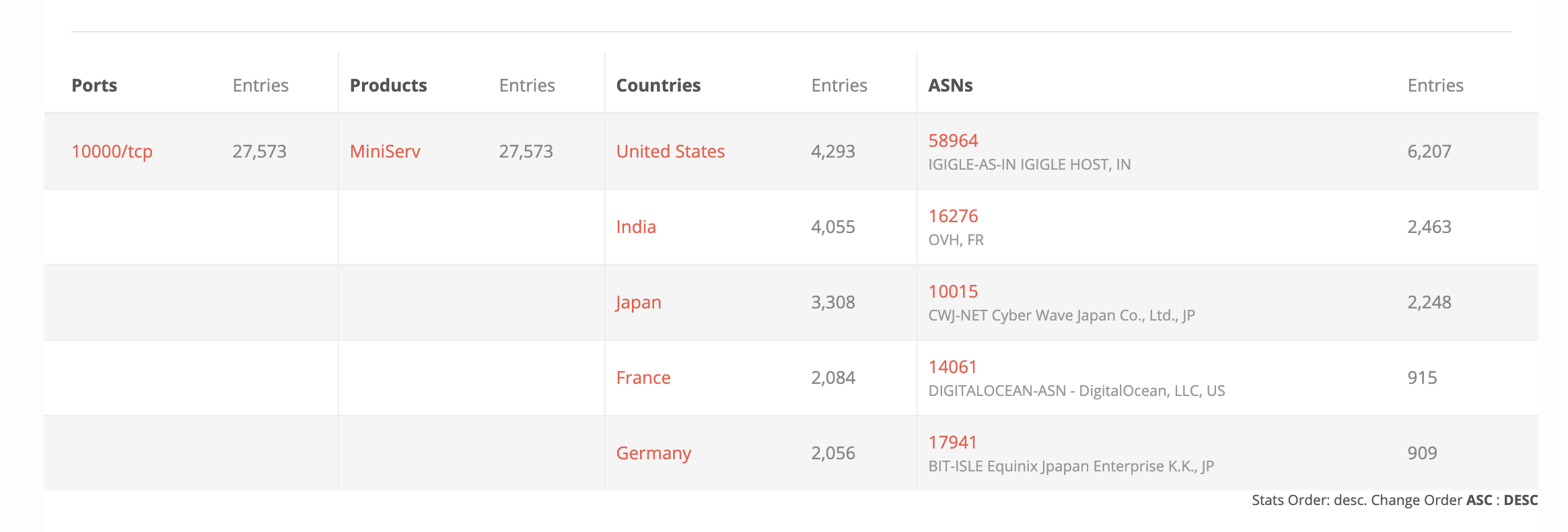
The security notice indicates that version 1.890 (CVE-2019-15231) is vulnerable in the default configuration, while the other affected versions require the “user password change” option to be enabled. According to a BinaryEdge search, there are nearly 28,000 publicly accessible systems running version 1.890 of webmin.
Analysis
An attacker can send a malicious http request to the password reset request form page to inject code and take over the webmin web application. According to the vulnerability writeup, an attacker does not need a valid username or password in order to exploit this flaw. The existence of this feature means this vulnerability has potentially been present in Webmin since July 2018.
"Webmin 0day remote code execution"
— Shishi0_ (@shishi0_) August 17, 2019
Tl;Dr: Lack of input validation in the reset password function allows RCE (CVE-2019-15107). Over 13 0000 vulnerable on Shodan.
PoC:
/password_reset.cgi
user=root&pam&expired&old=wrong | idhttps://t.co/kYKfq8v6Bb
According to a Webmin release note, the company’s security team “...received no advance notification of it, which is unusual and unethical on the part of the researcher who discovered it. But, in such cases there's nothing we can do but fix it ASAP.” While not entirely unheard of, unannounced public disclosures of vulnerabilities are uncommon, even at DEF CON, especially when the organization in question has a cash bug bounty program, as Webmin does.
Confirmed by Webmin team now. 1.882 - 1.920 contain RCEs introduced due to compromised build infrastructure.
— Roman (@faker_) August 18, 2019
1.890 contained the real deal: Remote unauthenticated code execution with default config (commands executed as root).
Compromised builds date back until July *2018*! https://t.co/SgqJN2EI5l pic.twitter.com/xznHPk2IjP
This vulnerability disclosure comes on the heels of CVE-2019-12840, another RCE vulnerability that was disclosed by AKKUS back in June 2019. Webmin has stated for CVE-2019-12840, “This is NOT a workable exploit as it requires that the attacker already know the root password. Hence there is no fix for it in Webmin.”
Proof of concept
AKKUS has posted a full writeup with a detailed explanation of proof of concept code and an exploit module.
Solution
Updating to Webmin 1.930 or disabling the “user password change” option in Webmin will mitigate CVE-2019-15107, but restricting "Package Updates" module access is the only mitigation step available to prevent exploitation of CVE-2019-12840. Additionally, the Webmin team has noted that 1.930 addresses some cross-site scripting (XSS) vulnerabilities as well and encourages users to upgrade even if the password expiry policy option is not in use.
Identifying affected systems
A list of Nessus plugins to identify these vulnerabilities will appear here as they’re released.
Get more information
- Webmin security advisory page
- AKKUS page for CVE-2019-15107
- AKKUS page for CVE-2019-12840
- Webmin advisory notification page
- Tenable plugin search page
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 60-day trial of Tenable.io.
Learn more
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success