As the NVD scales back CVE enrichment, here’s what Tenable customers need to know

NIST’s shift toward selective CVE enrichment creates significant visibility gaps for teams relying solely on the National Vulnerability Database. As AI accelerates vulnerability disclosure rates, organizations need independent, high-fidelity intelligence to prioritize risks that the NVD may now overlook.
Key takeaways
- NIST is pivoting to a prioritized enrichment model, focusing only on specific criteria like the CISA KEV catalog and federal software, which leaves a growing backlog of unenriched vulnerabilities.
- Tenable remains unaffected by these changes because it doesn’t depend on the NVD to develop checks and scoring metrics.
- Contextual intelligence is now a requirement for survival, as Tenable identifies significantly more "exploited in the wild" vulnerabilities and provides quick identification of known exploited vulnerabilities.
The National Institute of Standards and Technology (NIST) will no longer attempt to enrich all CVE entries in the National Vulnerability Database (NVD). The decision, announced last week, is bad news for organizations that depend entirely or primarily on the NVD for vulnerability metrics. It’s also a negative for organizations whose vulnerability scanning program relies on the Common Platform Enumeration (CPE) enrichment that is included in the NVD records.
Instead, NIST said it will prioritize for enrichment the CVEs that meet the following criteria:
- CVEs appearing in CISA’s Known Exploited Vulnerabilities (KEV) Catalog
- CVEs for software used within the federal government
- CVEs for critical software as defined by the 2021 Executive Order 14028
NIST’s decision was driven by the skyrocketing number of published CVEs, a years-long trend that is expected to continue to intensify, as AI accelerates the pace of vulnerability discovery and disclosure. In 2025, the annual record was broken again with more than 40,000 published CVEs. About two years ago, NIST acknowledged that it was struggling to enrich all CVEs, leading to a big backlog.
What does this mean for Tenable customers?
We have written in the past about previous delays in NVD enrichment and about the concerns raised when the CVE program was at risk of losing funding. As was true then, Tenable does not depend on NVD for scoring metrics or for developing checks for vulnerabilities. We have developed our own internal Vulnerability Intelligence Database which drives our internal prioritization and content. This database is also available in our products to help customers better prioritize remediation efforts and understand the full context required to understand the risk presented by a new vulnerability.
From our vulnerability intelligence we can also better understand some of the implications of this prioritization strategy and where the gaps might become problematic. While the CISA KEV is a great resource, its more limited scope and selection criteria means that some exploited vulnerabilities do not make the list. Specifically, based on our own intelligence, we track an additional 355 vulnerabilities as exploited in the wild -- 1,924 compared to the CISA KEV’s 1,569 currently. Additionally, we have a median lead time of 3.2 days for identifying known exploited vulnerabilities. When time-to-exploit is measured in days or even hours, rather than weeks, 3.2 days can make a significant difference in staying ahead of attackers.
Additionally, because we develop our vulnerability coverage directly from vendor advisories rather than depending on NVD or MITRE, we’re able to deliver accurate and timely checks for emerging vulnerabilities. This data also helps to build out our vulnerability intelligence so that we have comprehensive contextual data that would typically be pulled from NVD – data such as CVSS metrics, valuable references, and affected products and fixed versions.
What the NVD delays mean for security teams
Ongoing dependence on NVD for vulnerability data has always had its limitations given existing delays. While NIST’s new CVE-enrichment strategy aims to take a risk-centric approach, we can see that there are likely to be critical gaps – and those gaps create real risk for security teams.
Thus, as the pace of vulnerability disclosures and real-world exploitations accelerates, further fueled by AI, security teams must have access to a reliable source of contextual intelligence to make the rapid, informed prioritization decisions necessary to protect their environments.
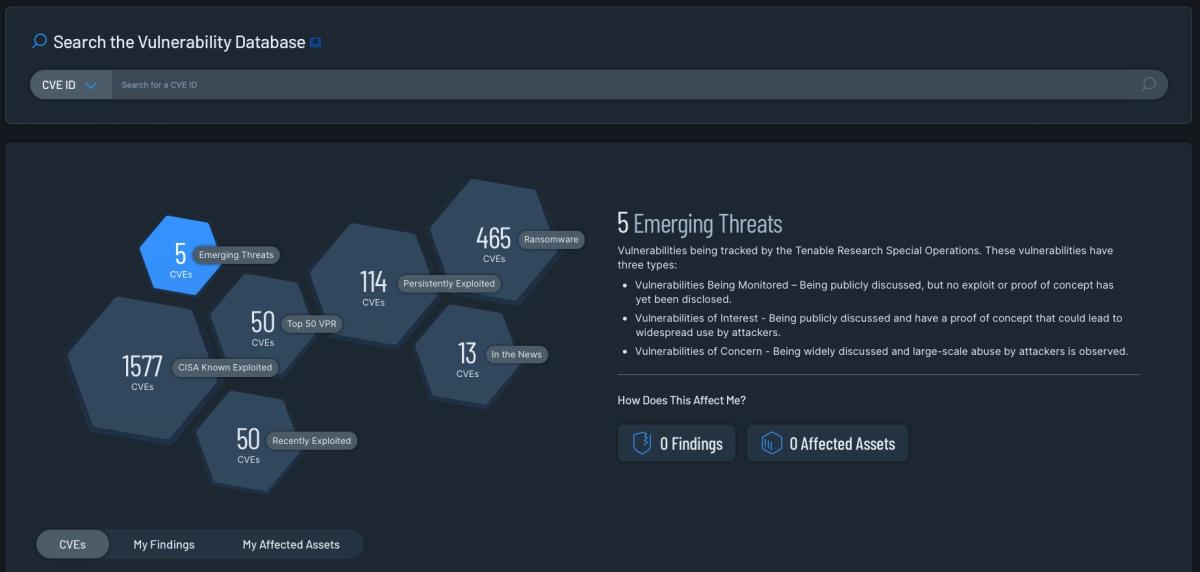
Tenable Vulnerability Management's vulnerability database search interface
With Tenable’s Vulnerability Intelligence, it is possible to quickly understand the real world risk that a vulnerability presents based on available proof of concept data, evidence of real world exploitation, association with ransomware, and many other critical data points. Vulnerability Intelligence is available in Tenable Vulnerability Management,Tenable Security Center and Tenable One.
Additionally, that same contextual data is incorporated into Tenable Cloud Security and the Tenable One Exposure Management Platform enabling teams to quickly focus on the highest risk vulnerabilities. Tenable One compiles a comprehensive asset inventory of your environment, allowing you to check which of your applications have, for example, a recently disclosed zero-day vulnerability. Because Tenable One brings together all of the data from multiple sensors into a single unified view, it can help you understand important context like account privileges, external exposure, asset properties, attacker pathways, and more. In short, Tenable One gives you full visibility across your entire infrastructure, helping you understand where your organization is exposed, and prioritize remediation based on which targets present the most significant risk.
Meanwhile, Tenable’s Vulnerability Prioritization Rating (VPR) wraps all of this contextual data up into a score that can be used for prioritization based on either the numeric score or the risk rating (low, medium, high, critical). VPR uses machine learning algorithms to predict the likelihood of exploit activity in the subsequent 28 days and incorporates threat intelligence, vulnerability characteristics, and insights from the Tenable Research Special Operations team to pinpoint the critical 1.6% of vulnerabilities that represent actual risk. By joining the contextual data about the vulnerabilities with the Asset Criticality Rating (ACR) of affected assets, you can quickly go from triage to informed prioritization and remediation action, reducing the risk of exploitation.
Learn more
Learn more
- Exposure Management
- Risk-based Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success