New In Nessus: Find and Fix These 10 Active Directory Misconfigurations

Let's face it: Active Directory is a feeding frenzy for hackers. Here's how our updated Nessus scan engine can help you disrupt attack paths.
Active Directory (AD) has been the leading identity and access management solution for organizations over the past 20 years. It's an impressive lifespan for a product that hasn't fundamentally evolved since its first release.
Such stability is commendable and has allowed Active Directory users — a whopping 90% of the Global Fortune 1000 — to implement longlasting authentication and authorization strategies rooted in solid ground.
On the downside, this stability gave plenty of time for threat actors to skill-up and design equally solid AD-centric attacks from external and internal positions alike. The situation is compounded by the fact that most organizations designed their AD implementations years ago and rarely revisit them with an eye toward present-day security threats..
Today, let's face it: AD is a feeding frenzy for hackers.
Behind every headline-grabbing breach or critical infrastructure-crippling ransomware attack is a misconfigured AD deployment. Ok, maybe not all of them, but the vast majority of attacks — whether sophisticated or by-the-book — require flaws in AD which allow an attacker to move laterally and gain those all-important admin privileges.
If cybercrime is an existential threat to our society, then all organizations need to be informed immediately of the state of (in)security of their AD. Only then will they be able to truly align their security tactics with the reality of their threat landscape.
This is why Tenable recently acquired Alsid and released Tenable.ad. We understand how AD plays a critical role in managing single sign-on processes and the level of access users are granted once authenticated. Tenable.ad provides holistic AD security enabling you to find and fix existing weaknesses and detect ongoing attacks in real time without the need to deploy agents or use privileged accounts. And when combined with our industry-leading Risk-based Vulnerability Management solution, Tenable.ad can disrupt the attack path, ensuring attackers struggle to find a foothold and have no next step if they do.
Today, we're going a step further in our AD security journey. We have incorporated 10 foundational AD checks directly in Nessus. Now, users of Nessus Essentials, Nessus Professional, Tenable.sc, Tenable.io and Tenable.ep can detect commonly exploited weaknesses to help protect credentials and prevent privilege escalation. These plugin checks generally fall into two categories:
- Password and credential protection to help prevent attackers from implementing brute-force attacks on credentials and impersonating other users or accounts.
- Privilege escalation and lateral movement to limit the ability for attackers to obtain excessive rights or privileges to move across domains.
The full list of AD plugins are as follows:
Password and Credential Protection
| Plugin name | Description |
|---|---|
| Kerberoasting | A Domain admin or Enterprise admin account is vulnerable to the Kerberoasting attack.
|
| Weak Kerberos encryption | The Kerberos encryption is too weak on one user account leading to potential credential theft.
|
| Kerberos pre-authentication validation | The Kerberos pre-authentication is disabled on one user account leading to potential credential theft.
|
| Non-expiring account password | A user account may never renew its password.
|
| Unconstrained delegation | Unconstrained delegation is allowed on a computer account allowing potential credential theft.
|
| Null sessions | The Anonymous or Everyone group is part of the "Pre-Windows 2000 Compatible Access " allowing null session attacks.
|
Privilege Escalation and Lateral Movement Prevention
| Plugin name | Description |
|---|---|
| Kerberos KRBTGT | The Kerberos master key is too old and could be used as a backdoor.
|
| Relação de confiança perigosa | No security mechanism has been activated on a trust relationship allowing lateral movement across AD domains.
|
| Primary Group ID integrity | A potential backdoor using the Group ID has been found on a user account.
|
| Blank passwords | A user account may use a blank password to authenticate on the domain.
|
In addition to the new AD plugins, we have also created a new scan template (Active Directory Starter Scan) and a preconfigured dashboard (Getting Started with Active Directory Security) to help you easily discover and analyze these basic AD weaknesses. The new AD plugins and scan template are available in Nessus Essentials, Nessus Professional, Tenable.sc, Tenable.io and Tenable.ep. The new preconfigured AD security dashboard is available today in Tenable.sc and will be available in Tenable.io and Tenable.ep on August 5.
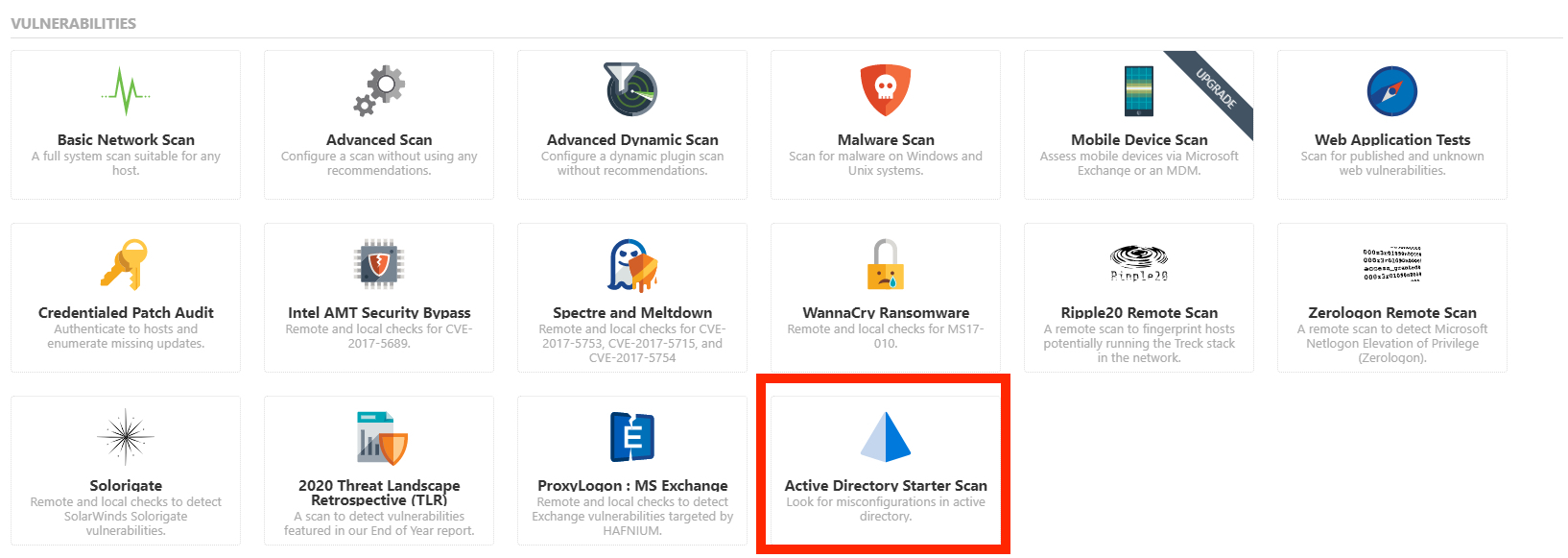
Tenable has created a new scan template to support AD security.
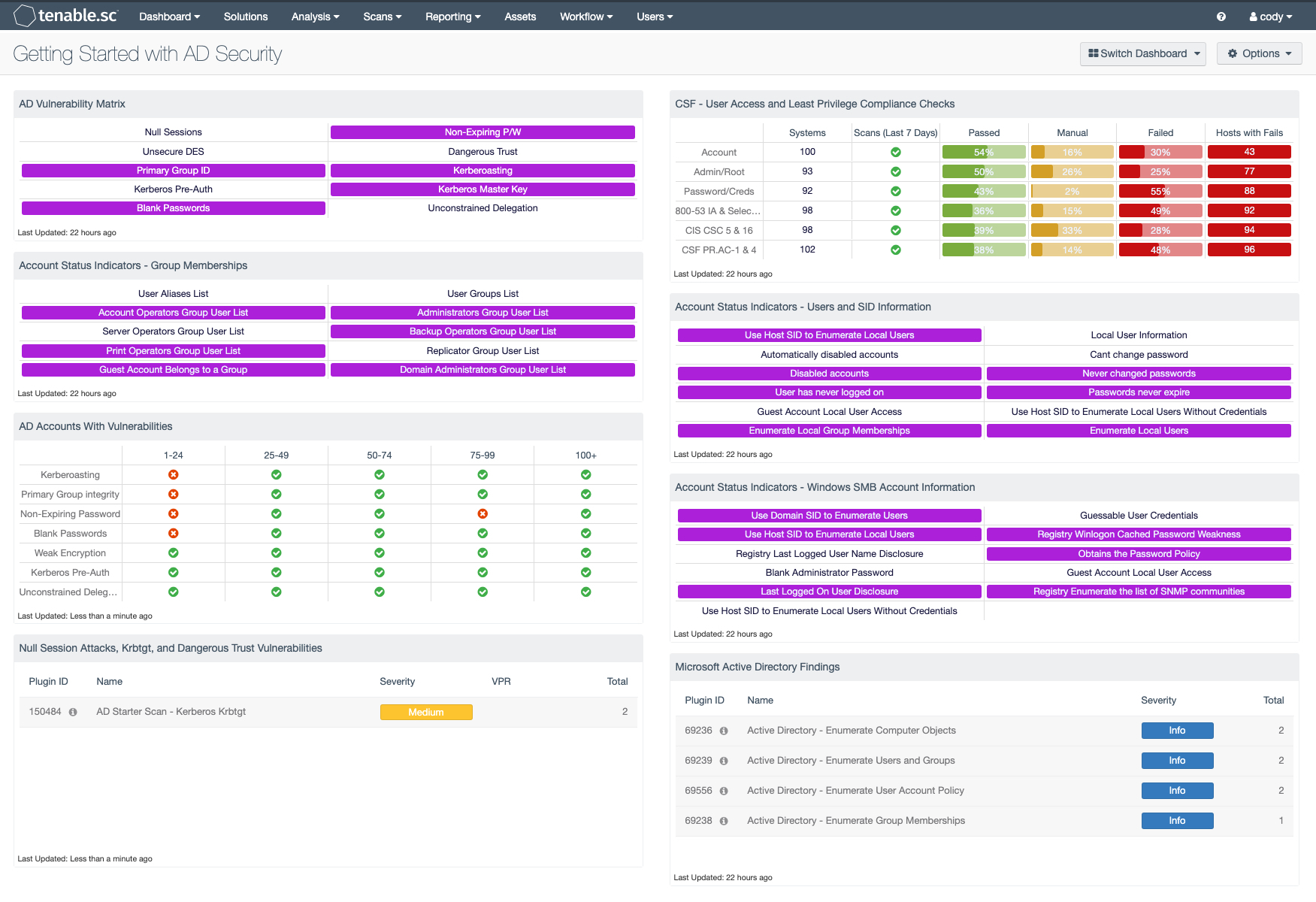
Example of the new pre-configured Tenable dashboard for getting started with AD security.
These new AD security capabilities in the Nessus scan engine are a great first step toward disrupting attack paths before you are ready to embark on a more comprehensive AD security program.
While we're on the topic of AD security, we're excited to announce the release of Tenable.ad 3.1 with a number of enhancements to help you detect critical Indicators of Attack (IoA) faster. New filters and visualizations help threat hunters accelerate their efforts to isolate malicious behavior and turn attacks into attempts.
Learn more
- Register for our upcoming Customer Update webinars to learn more about these new AD plugins: Tenable.io, Tenable.sc and Nessus.
- Visit https://www.tenable.com/products/tenable-ad to learn more about AD security or to request a demo of Tenable.ad.
Learn more
- Active Directory
- Announcements
- Risk-based Vulnerability Management
- Threat Management
- Vulnerability Management
- Vulnerability Scanning


Tenable One
Solicite uma demonstração
A plataforma líder mundial em gerenciamento de exposição com tecnologia de IA.
Obrigado
Agradecemos seu interesse pelo Tenable One.
Um representante entrará em contato em breve.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success