How VPR Helped Prioritize the Most Dangerous CVEs in 2019
How do VPR and CVSS compare when assessing the most dangerous CVEs in 2019? Let’s find out.
Two weeks ago, we kicked off a blog series on vulnerability priority rating (VPR), with a post focused on the characteristics of VPR that differentiate it from CVSS. In this post, we will demonstrate how VPR can be used to target the most dangerous vulnerabilities that exist in your network.
The riskiest vulnerabilities based on industry reports
It is common for organizations to publish lists of the most dangerous vulnerabilities based on their own telemetry and analysis. For this analysis, we examine the most dangerous CVEs of 2019 based on publications by Recorded Future, SonicWall and Verint. Their respective ratings capture different aspects of threats: threats from advanced persistent threat (APT) activities, threats from attacks in the wild and threats captured from the web.
We will look at how VPR could have helped target the riskiest vulnerabilities in the threat landscape. First, a quick note on the industry reports:
- Recorded Future applies analytics algorithms to a variety of web-based threat content. Their rating of the most dangerous vulnerabilities in 2019 represents a broad assessment of threat.
- Sonic Wall discussed the top 10 most exploited CVEs based on analytics of attack signatures.
- Verint identified a list of the most exploited old CVEs by APT in 2019.
Overview: A look at the data
The three reports highlight the 31 most dangerous CVEs in 2019, affecting 76 products from 18 vendors. Around 40 percent relate to Microsoft products while the remainder are split across 17 other vendors (see Figure 1).
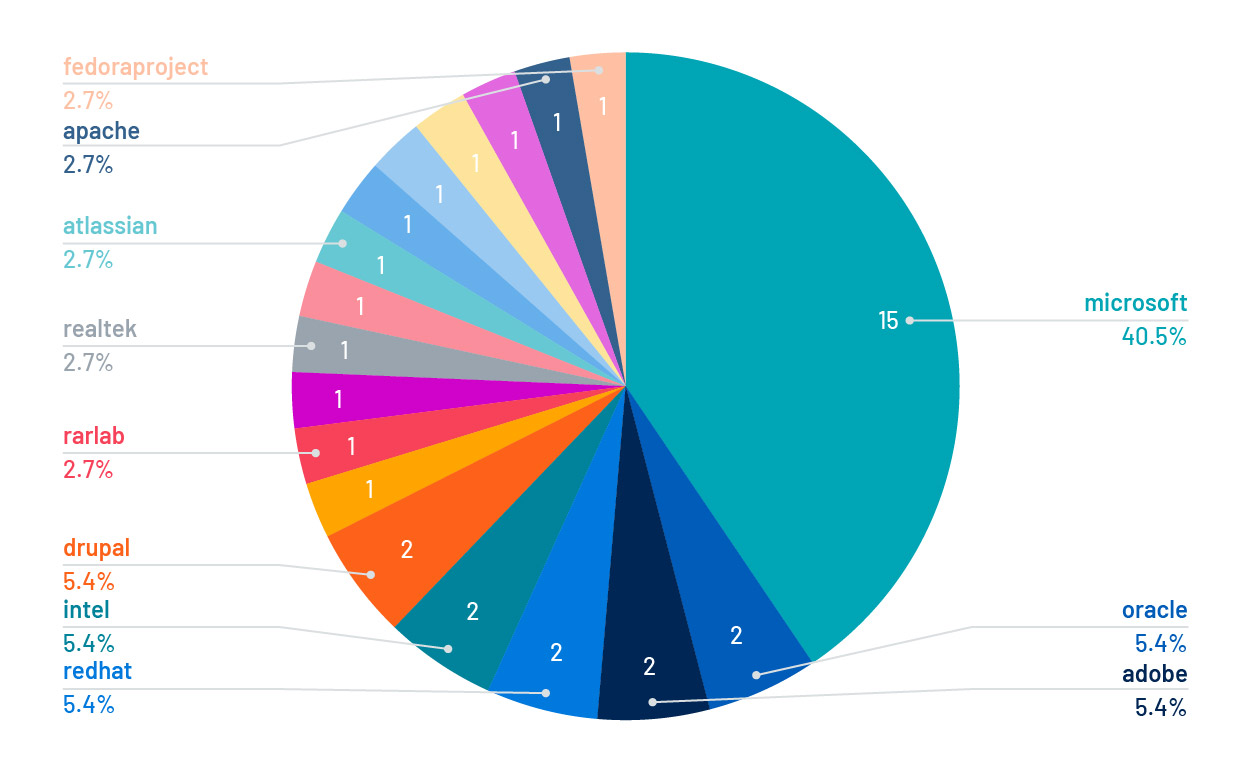
Figure 1. Most dangerous CVEs in 2019 by vendors
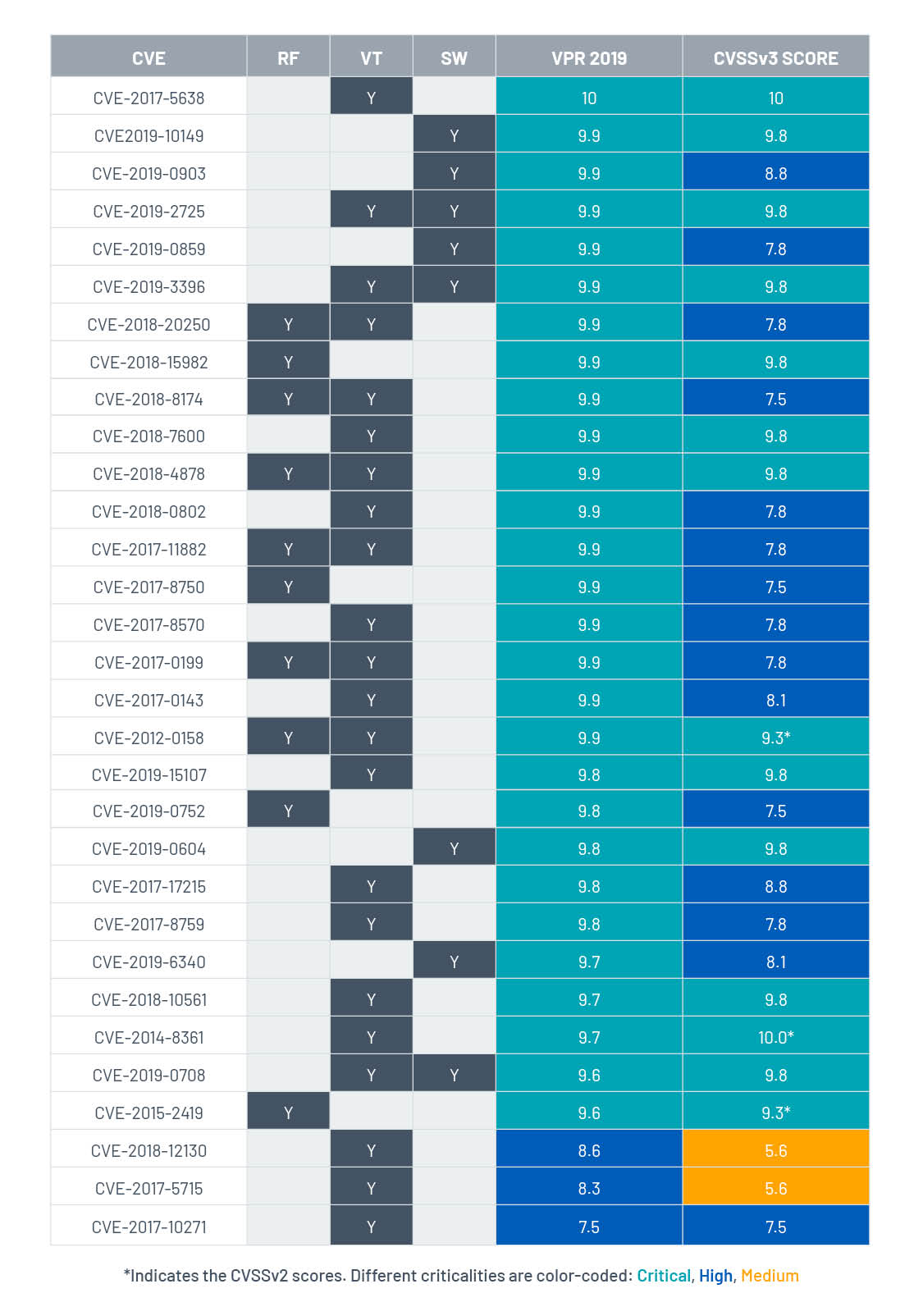
Table 1 lists all the CVEs included in the three reports, ordered by VPR score. The RF (Recorded Future), SW (SonicWall) and VT (Verint) columns indicate the report where each CVE is listed. In general, VPR is better at reflecting the threat of the CVEs than CVSS:
- 28 (90%) of the vulnerabilities are rated VPR Critical with a 9.6 minimum score – this VPR score would typically win a spot in the top 100 highest-priority vulnerabilities for remediation. CVSS rates 14 vulnerabilities as Critical, including 11 by CVSSv3 and three by CVSSv2 (which have no CVSSv3 score). The minimum CVSSv3 score for these vulnerabilities is 9.8. Technically, this is a high CVSSv3 score, but not enough to stand out from the crowd of 8,700 CVEs with the same and higher CVSSv3 score.
- Some vulnerabilities from these lists were not rated Critical by VPR or CVSS. Of these, three are rated VPR High and 15 are rated CVSS High. None are categorized as VPR Medium and two are rated CVSS Medium. The last section of this post is dedicated to the discussion of the reason and methods for mitigation.
Table 1. Most dangerous CVEs of 2019
Do not overlook local vulnerabilities
A common misconception is that the most exploited vulnerabilities are associated with remote attacks (attack vector = network [AV:N]). The statistics, however, tell a slightly different story. Nearly a third of these vulnerabilities are exploited locally (attack vector = local [AV:L]) via phishing campaigns or spam emails, for example. See Figure 2.
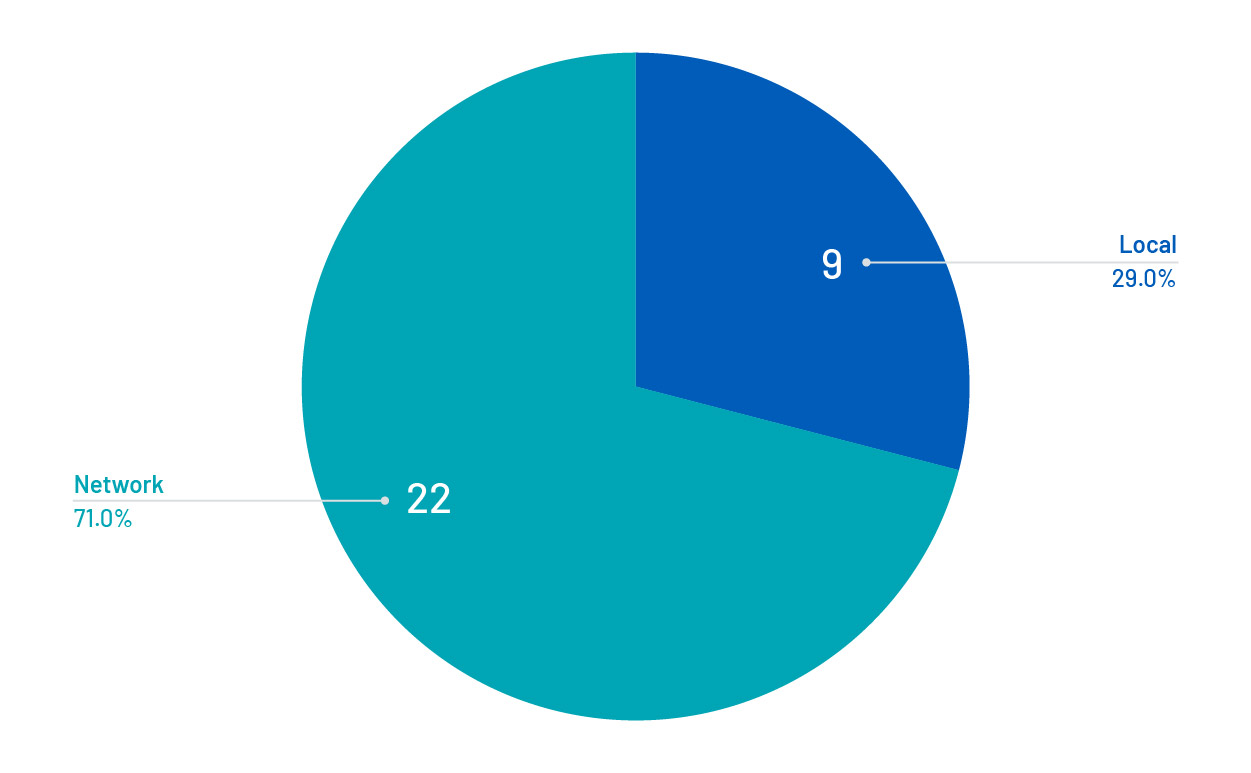
Figure 2. Most dangerous CVEs in 2019 by attack vectors
As shown in Table 2, the average CVSSv3 score for CVEs with a local attack vector is 7.3, but 9.0 for the remotely exploitable vulnerabilities. This difference is due to the fact that the CVSS scoring formula gives a lower weight to AV:L than AV:N. This can result in locally exploited vulnerabilities being excluded from remediation plans based on their CVSS score. In fact, there is only one configuration that could generate a Critical CVSSv3 score for a locally exploited CVE: AV:L/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H.
Table 2. Comparing average VPR with CVSS for the most dangerous CVEs in 2019, broken out by attack vector
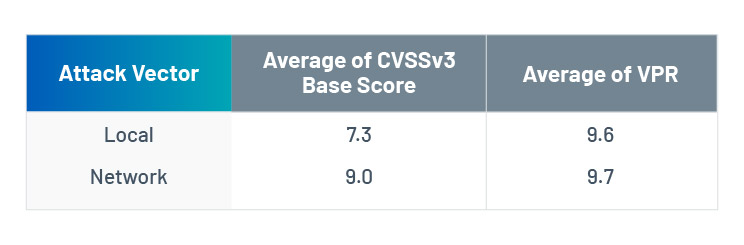
On the other hand, VPR does not penalize vulnerabilities with local attack vectors. Notice that there’s little difference in the average scores based on the attack vector. This means, VPR can bubble up the most threatening vulnerabilities irrespective of attack vector.
CVE-2017-11882: Microsoft Office vulnerability
One example is the Microsoft Office vulnerability, CVE-2017-11882, which was selected as one of the most dangerous CVEs in 2019. Exploitation of this CVE is often associated with phishing emails. Successful exploitation can run scripts to download, execute and persist backdoor trojans on the target host. Although a patch was released in 2017, this CVE remains under constant threat. In June 2019, it was reported as being under active exploitation by cybercriminals targeting European countries. IBM researchers have also found evidence of it being actively targeted in their honeypot systems in 2019. This year, there are reports of it being used in phishing campaigns in the pandemic of COVID-19. Based on Tenable scan telemetry, we estimate that eight percent of our customers are still affected by this vulnerability.
Considering the persistent threat against it, this CVE should be one of the first patched following detection in your network. CVSSv3 rates this CVE as 7.8 because successful exploitation needs to be performed locally and requires user interaction. As a result, such a CVSSv3 score would rank CVE-2017-11882 behind 18410 other CVEs for remediation. On the flip side, the VPR for this CVE is 9.9, flagging it as a top priority.
Threat is more than being popular on the web
Not all these CVEs came under the spotlight in 2019. Google Trends is a great tool for assessing the popularity of search terms. It provides weekly popularity scores for search terms you input. The scoring is relative, with the most popular term scoring 100 at its peak. The other search terms are scaled between 0 and 99.
We pulled Google Trends popularity scores for all the 31 most dangerous CVEs. The Top 5 most popular CVEs based on Google Trends were:
- CVE-2019-0708
- CVE-2019-2725
- CVE-2019-0604
- CVE-2019-10149
- CVE-2018-12130
Figure 3a compares their weekly popularity scores during 2019. CVE-2019-0708 (BlueKeep), Microsoft’s Remote Desktop Protocol vulnerability, received widespread attention following disclosure in mid-May.
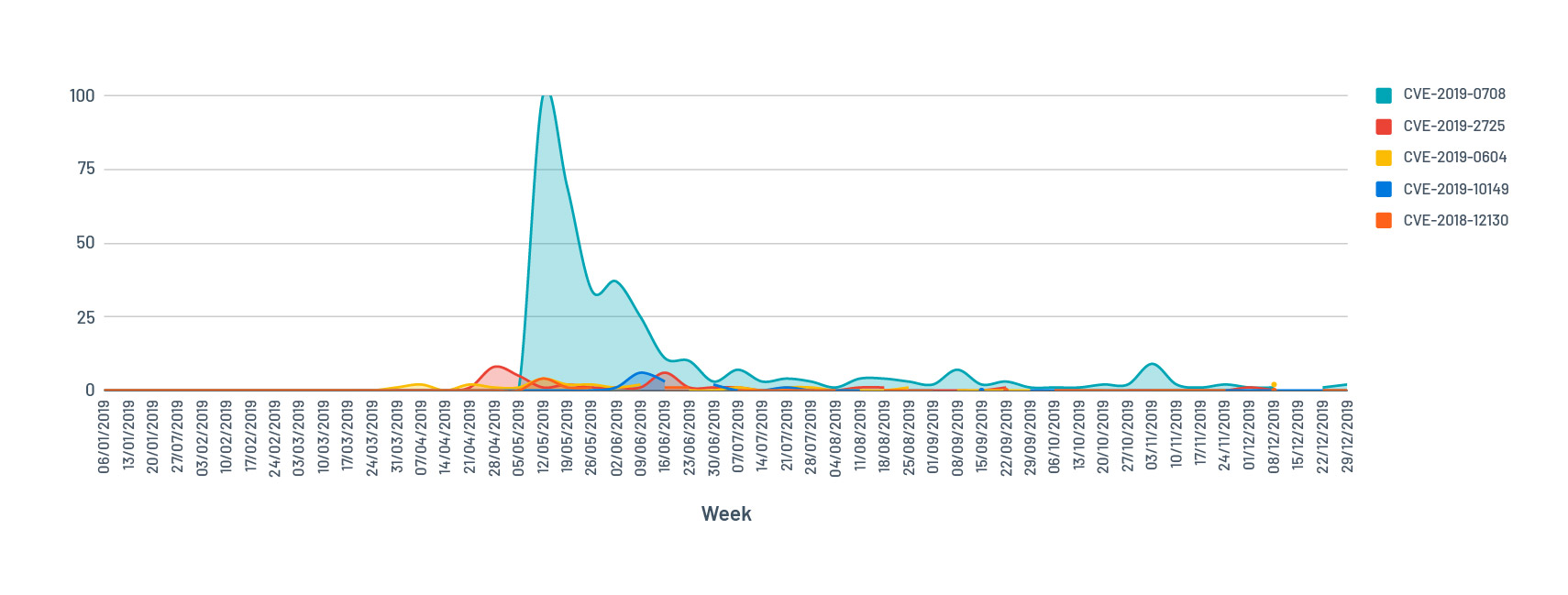
Figure 3a. The top 5 most popular CVEs based on Google Trends
The popularity of CVE-2019-0708 (BlueKeep) was so great in 2019 that it dominates Figure 3a, making the trend lines of other CVEs become hardly distinguishable from zero. To better illustrate the trend of popularity for other CVEs, we excluded the top three most popular CVEs from the search and redid the chart (see Figure 3b). CVE-2019-10149 and CVE-2018-12130 are included in Figure 3b as references for scale between the two charts.
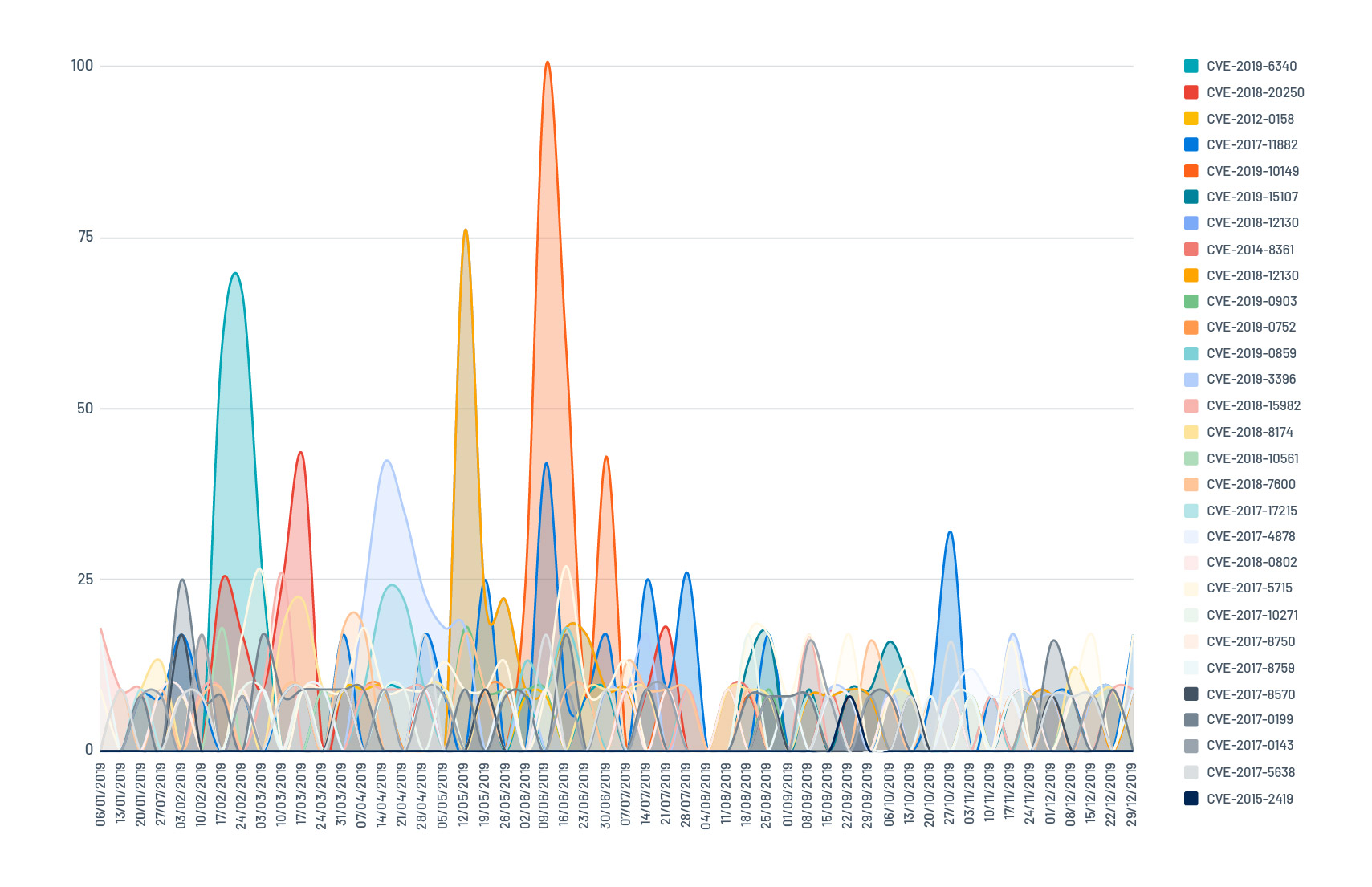
Figure 3b. CVE popularity by Google Trends excluding the top 3 most popular CVEs
These CVEs fall into two groups:
- Group 1: CVEs with noticeable spikes during 2019, corresponding to lots of hype on the web.
- Group 2: CVEs that went under the radar in 2019 (lost in the noise at the bottom of Figure 3b). Six CVEs belong to this group: CVE-2012-0158, CVE-2019-0752, CVE-2017-17215, CVE-2018-0802, CVE-2017-8750 and CVE-2015-2419. These are the vulnerabilities to watch out for. They face constant attacks from threat actors in the wild, but manage to escape widespread recent media attention. These vulnerabilities are usually highly weaponized and can be exploited relatively easy by cybercriminals. All six of these vulnerabilities are rated as VPR Critical. But, only four of the six are rated Critical based on CVSSv3.
Dangerous CVEs not rated to be VPR Critical
Three of the most dangerous vulnerabilities in 2019 did not receive a VPR Critical rating:
- CVE-2018-12130 (VPR 8.6)
- CVE-2017-5715 (VPR 8.3)
- CVE-2017-10271 (VPR 7.5)
In part 1 of the blog series, we explained that VPR is composed of a technical impact component, which is taken from the CVSSv3 impact score, and a threat component generated from our machine-learning-based threat model. In this case, all three vulnerabilities were assigned low impact subscores. The low impact component essentially anchors the VPR score to be below 9 based on the scoring model.
As VPR is a composite score, the weights assigned to the various components is an ongoing topic. So, while VPR on its own can be used as filtering criteria for vulnerability remediation efforts, it is not the only factor to consider. Sometimes, when considering other factors, there might be a trade-off:
- What is the impact score of the vulnerability?
- How mature is the exploit code?
- Has there been recent threat activity?
- What were the threat sources?
The VPR drivers, which we’ll explore later in this blog series, can help refine the decision- making process.
Key takeaways
In this post, we compared VPR with CVSS scores for the most dangerous 31 CVEs reported by Recorded Future, SonicWall and Verint in 2019. VPR rated 28 as Critical while CVSS rated 14 as Critical.
Looking at these CVEs from different angles, we saw that vulnerabilities with a local attack vector are as dangerous as those with a network attack vector, but could get neglected if you follow CVSSv3 scores alone for remediation. VPR allows these locally attacked dangerous vulnerabilities to be prioritized as Critical vulnerabilities based on high threat against them.
Moreover, dangerous vulnerabilities are not always the ones that make the headlines. By looking at Google Trends, we noticed six dangerous CVEs did not come under the spotlight in 2019. Hence, identifying and remediating the most dangerous CVEs based on web popularity is not reliable. These CVEs might have had their taste of the limelight, but would require security researchers to spend time digging into their history. Instead, the use of multiple threat sources and exploit code maturity allows VPR to identify vulnerabilities with stealth threats.
Finally, we talked about the importance of using VPR scores with other criteria, like those offered as VPR drivers, for better decision making.
Get more information
- Start your free trial now to see VPR in action – available in Tenable.io (in the cloud) and Tenable.sc (on premises)
- Learn more about Tenable Predictive Prioritization and VPR
Learn more
- SecurityCenter
- Tenable Vulnerability Management
- Tenable Vulnerability Management (DO NOT USE)
- Threat Intelligence
- Vulnerability Management


Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success