Bridging the gap: How to integrate Claude Security into the Tenable One Exposure Management Platform

Bridge the gap between AI-driven vulnerability discovery and prioritized remediation. Learn how to integrate Claude Security’s deep-logic analysis into Tenable One to unify your attack surface, eliminate noise, and focus on the risks that matter most.
Key takeaways
- As frontier AI models like Claude accelerate the pace of vulnerability discovery, security programs must shift their focus toward efficient exposure prioritization and remediation to avoid drowning in noise.
- Integrating Claude Security with the Tenable One Exposure Management Platform allows teams to centralize deep-logic code analysis alongside the rest of the attack surface. This unified view helps normalize raw AI findings into actionable intelligence and a prioritized remediation plan.
- The integration process involves scanning code in Claude, exporting the findings, and using the Tenable Open Connector to map and aggregate data attributes. Proper aggregation ensures that vulnerabilities are grouped by root cause, preventing the artificial inflation of risk scores and allowing teams to focus on critical issues.
The promise of AI in security is compelling: find vulnerabilities faster than ever before. But speed of discovery alone doesn’t make organizations safer.
As AI tools like Claude Security surface complex, deep-logic vulnerabilities at an unprecedented scale, the bottleneck has quietly shifted. Discovery is no longer the hard part. Remediation and prioritization are.
Security teams are being buried under a surge of new vulnerability data. When AI-generated findings pile up in silos, disconnected from the rest of your attack surface, they don’t reduce risk. They add noise. And more noise means more time spent triaging instead of fixing.
To keep pace, organizations need to do more than discover faster. They need to normalize AI-driven findings against the rest of their attack surface to understand which ones actually pose a business risk.
By bringing Claude’s advanced code security insights directly into the Tenable One Exposure Management Platform via the Tenable One Open Connector, you can transform a flood of raw data into a unified, prioritized remediation plan.
Step 1: Run the security scan in Claude
The process begins by leveraging Claude’s deep-reasoning capabilities to perform a comprehensive security analysis of your codebase. Whether triggered via console or performed periodically, Claude Security can automatically identify complex logic flaws and vulnerabilities in a code repository of your choosing:

The first stage of the integration is generating raw security intelligence. Within the Claude Security interface, you’ll define the scope by connecting your target repository and selecting the appropriate branch (e.g., main). You can then choose the AI model used in the scan and the level of effort in which it should run.
In this example, we are using Claude Opus 4.7 with the effort level set to Extended for a comprehensive review. Keep in mind that the duration and cost of this scan will depend heavily on the complexity of your code repository.
Once Claude Security has finished analyzing your repository, you will be presented with a summary of the open security findings.

Step 2: Export the findings
To be able to ingest these findings within Tenable One, findings need to be exported. This can easily be done by clicking on the “Export all findings” option available within the scan screen and selecting Download CSV.

While a manual export is useful for initial validation and for the purposes of this review, manual processes cannot scale with the volume of vulnerabilities AI is capable of discovering. To truly bridge the gap, this workflow should be automated.
By leveraging Claude Security’s API webhooks and scheduled scans, you can automate the delivery of security findings directly to a secure cloud storage layer (such as Amazon S3). From there, the Tenable One Open Connector can be configured for continuous ingestion, ensuring your "single pane of glass" reflects your code’s security posture in near real-time without manual intervention.
Step 3: Set up the Tenable Open Connector
With the analysis complete, the focus shifts to centralizing that data within the Tenable Exposure Management platform. To account for the rapid evolution of AI-driven security tools, we utilize the Tenable One Open Connector. This approach allows security teams to seamlessly ingest Claude’s security findings into the Tenable platform, providing a versatile way to centralize AI-driven vulnerability data alongside the rest of your attack surface.
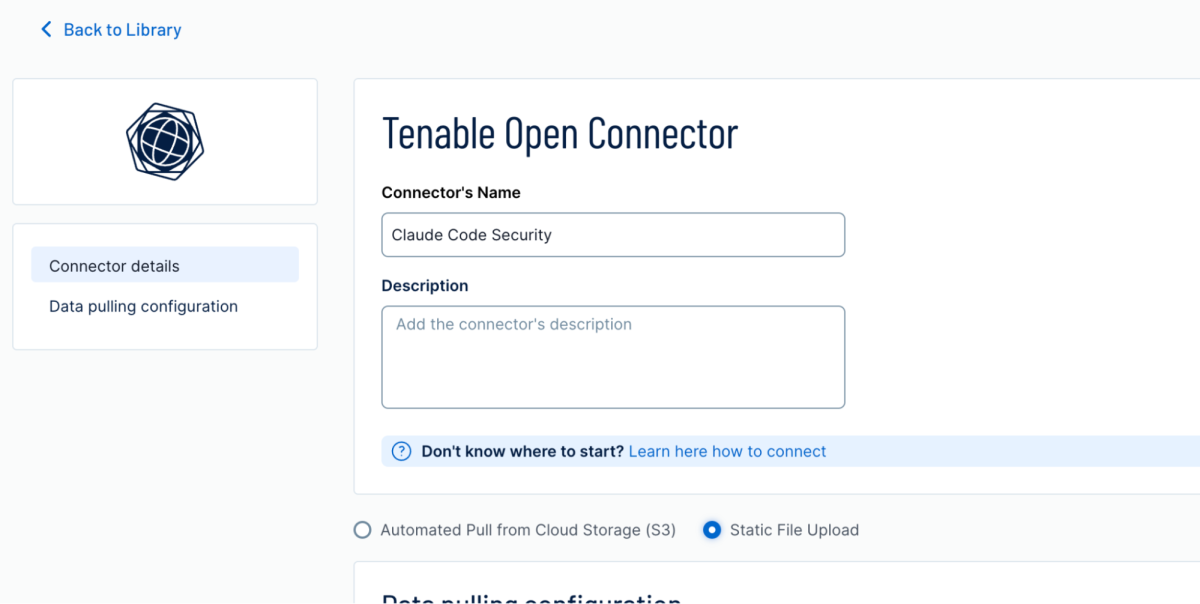
Within the Tenable One console, navigate to the Connectors management page to initialize a new Tenable Open Connector. We recommend a descriptive naming convention - such as "Claude Code Security" - to ensure clear attribution within your console.
To facilitate the data transfer, configure the connector with the following parameters:
- Data-pulling configuration: For uploading a single exported file, select the ״Static File Upload״ option.
- Data update mode: Select ״Override Data (Full Fetch):. This is a critical setting for maintaining data integrity. By selecting "Full Fetch," each new upload serves as the definitive source of truth. This ensures the platform completely refreshes your posture, automatically clearing remediated issues and preventing your dashboard from being cluttered by stale "ghost" vulnerabilities.
Step 4: Map the data attributes
This is the most critical phase of the integration. For Claude Security’s insights to be actionable, they must be translated from raw AI findings into the structured vulnerability language that Tenable One uses to calculate risk.
Upon uploading your Claude-generated CSV, you will be directed to the Attribute Mapping interface. This is where you define the relationships between Claude’s discovery fields and Tenable’s exposure attributes.
Based on Claude's output, you should configure the mappings as follows:
- Severity -> Severity
- Status -> Finding State
- Date created -> Asset Created Date
- Repository -> Asset Name
- Description -> Finding Description
- CWE -> Finding CWEs
- File path & Line -> Asset Generic Details (Custom)
- Finding URL -> Finding Generic Details (Custom)
- Name -> Finding Name
The final step is to define the uniqueness and aggregation logic. This tells Tenable One how to cluster individual findings so it can accurately calculate your Asset Exposure Score. Without proper aggregation, the same vulnerability found across multiple files could artificially inflate your risk score, creating the very "noise" we are trying to eliminate.
To ensure a clean data set, set the unique identifier to Finding Name.
By grouping based on the specific weakness identified, Tenable can consolidate multiple instances of a vulnerability into a single, high-context entry. This allows your security teams to focus on the root cause of the exposure rather than triaging hundreds of identical alerts. Once these logic parameters are set, you have successfully transformed Claude's raw AI discovery into a prioritized, enterprise-ready security asset.

Step 5: Execution and review
Once your mapping and aggregation logic are confirmed, click Save and Execute.
Your new integration will appear in the Connectors list with a "Connecting" status as Tenable One begins the initial ingestion and normalization process.
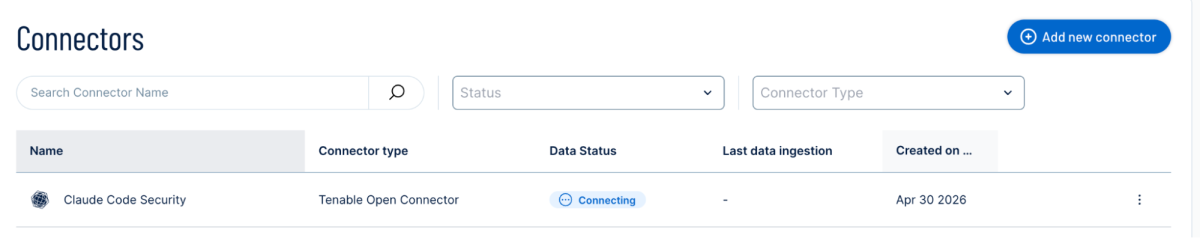
Within minutes, the "discovery bottleneck" begins to clear: Claude’s high-fidelity AI insights will populate your Tenable One dashboard, as distinct instances of weaknesses on your assets, fully integrated into your existing workflows and ready for prioritized remediation.
From AI discovery to actionable intelligence
By bridging Claude Security and Tenable One, you are doing more than just moving data between platforms - you are transforming a flood of raw AI findings into tracked, prioritized business metrics. Now you can understand how application code vulnerabilities may create new attack pathways or which ones are associated with revenue generating workloads. Static code risks will also inform resource decisions and executive communication as part of your exposure management governance to help you answer, "how secure am I" in this new AI-driven world.
In an era where AI can discover vulnerabilities faster than any human team can fix them, the goal of security operations has shifted. Success is no longer measured by the volume of your findings, but by the speed and accuracy of your response.
Why leave your most advanced security insights in a silo? By centralizing Claude’s deep-logic analysis within the Tenable Exposure Management Platform, you give your team the context they need to focus on what actually matters. You aren't just managing vulnerabilities; you are managing your entire attack surface from a single, unified source of truth.
Learn more
- Cloud
- Exposure Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success