Discover, prioritize, and remediate vulnerabilities, misconfigurations, identity,
and
data risks, across
multi-cloud environments.
-
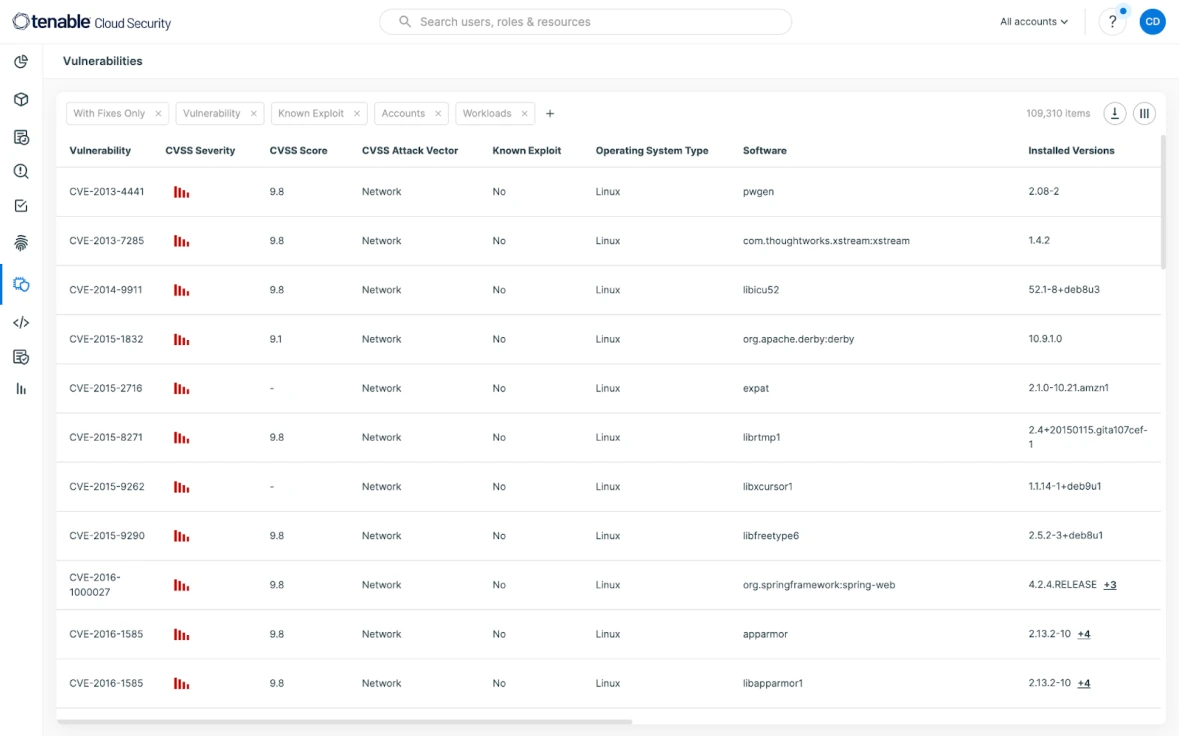
Cloud-Native Vulnerability Mgmt. Get prioritized visibility into every cloud resource
from development to runtime. -
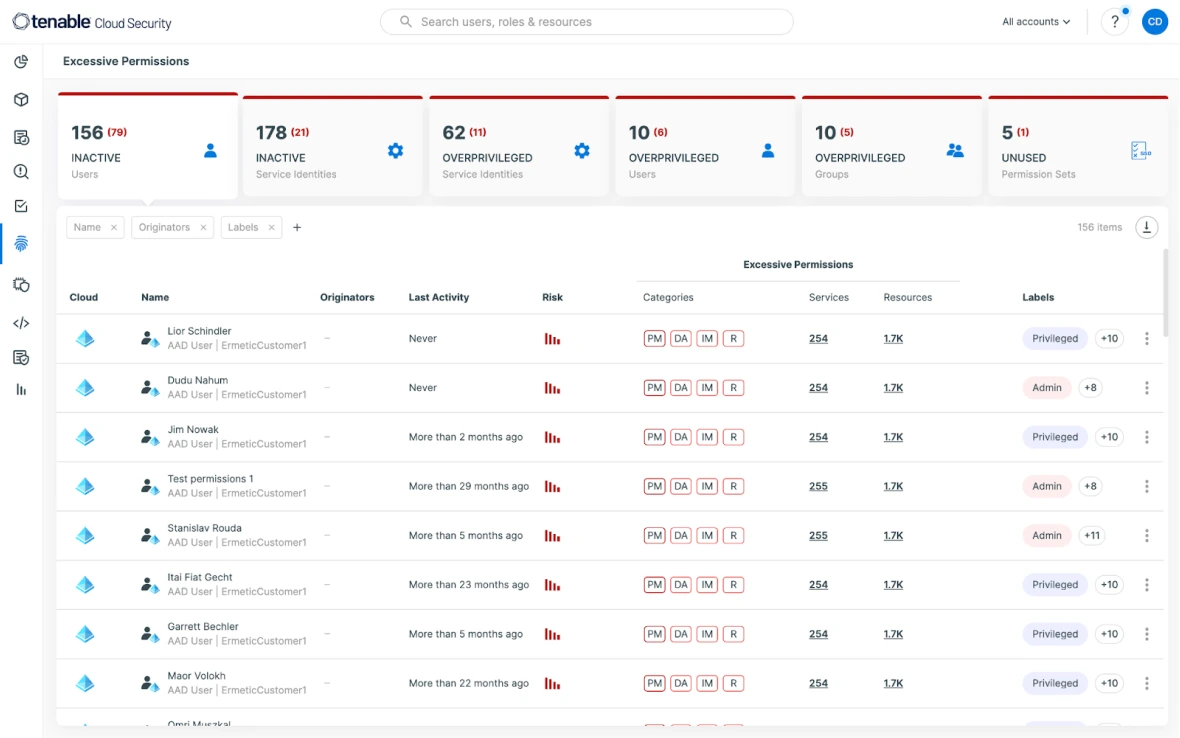
Enforce Least Privilege. Leverage the intuitive UI to attain the least privilege without disrupting productivity.
-
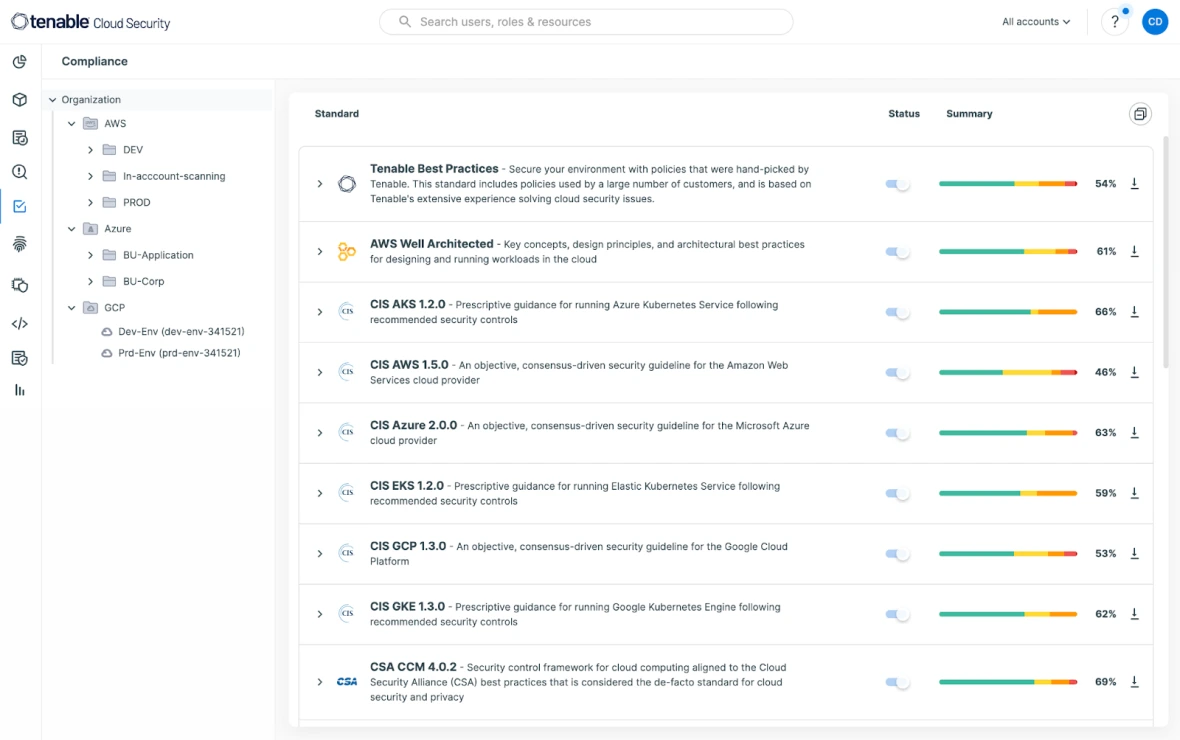
Automate Compliance. Eliminate audit fire drills. Verify and automatically
report on compliance frameworks.
Solicite uma demonstração do Tenable Cloud Security
Uma segurança de nuvem unificada extraordinária espera por você!
We'll show you exactly how Tenable Cloud Security helps you deliver
multi-cloud asset discovery, prioritized risk assessments and
automated compliance/audit
reports.
Join 40,000+ organizations automating their cloud security with the leading independent provider

Segurança da nuvem que se encaixa na sua jornada
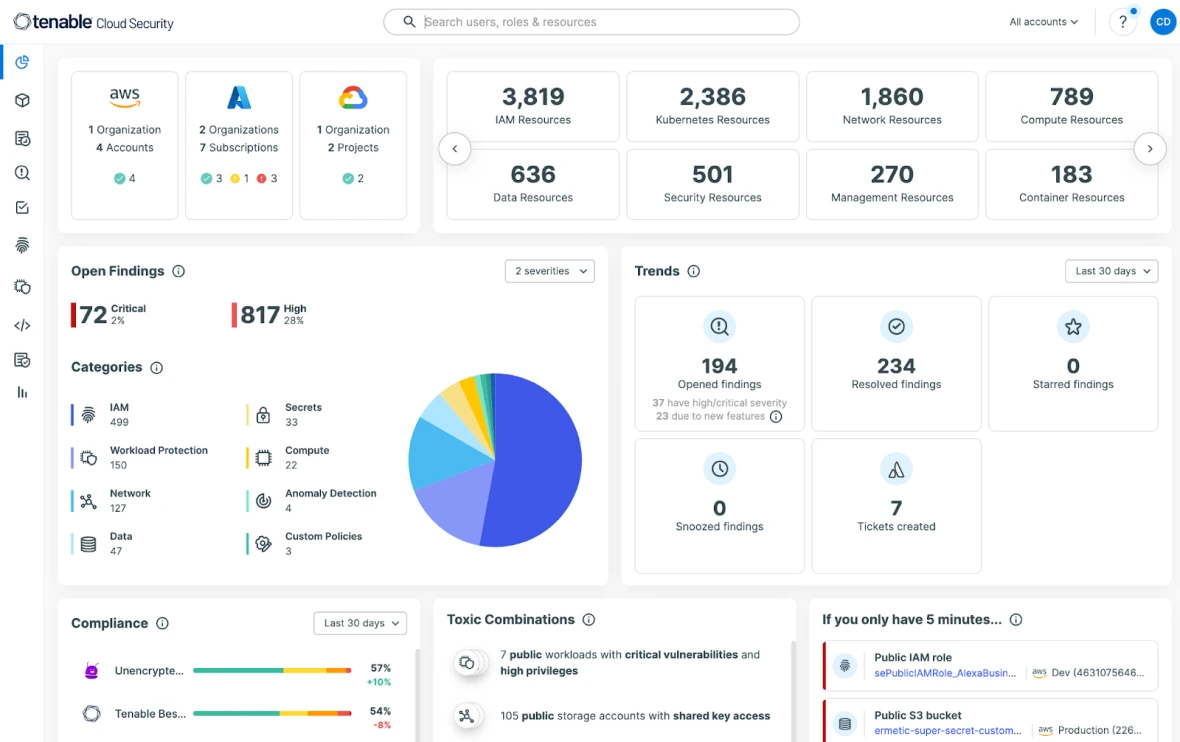
Get full visibility across AWS, Azure, GCP, and Oracle Cloud Infrastructure (OCI) with 100% agentless scanning. Continuously discover your cloud environment across infrastructure, workloads, identities, and data, powerfully visualizing all your cloud assets. Obtain a unified view that simplifies your team’s understanding of even the most complex issues.
Try for free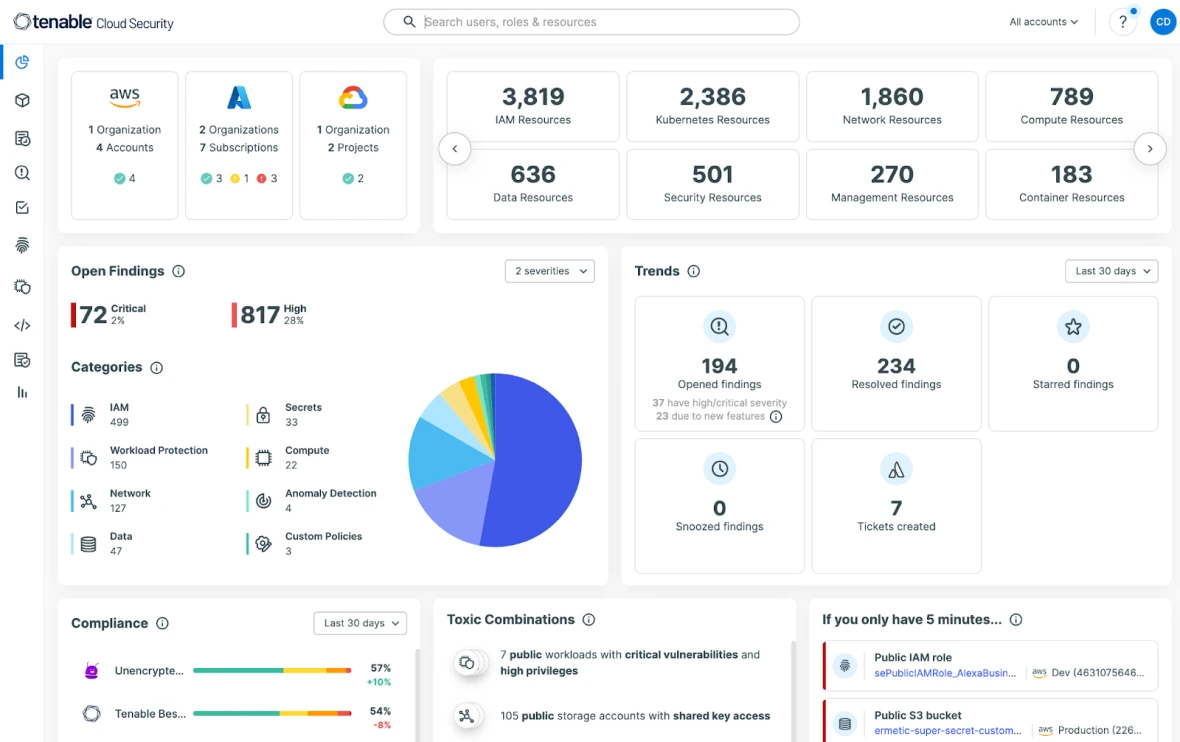
Monitore os riscos revisando e avaliando continuamente as definições e as configurações do ambiente de nuvem. Ao mapear os riscos descobertos em relação aos padrões e políticas de segurança, você pode atingir e manter a conformidade e lidar facilmente com auditorias em ambientes multinuvem. Aproveite os relatórios pré-criados para mais de 20 estruturas de conformidade, incluindo SOC-2, GDPR, PCI DSS, HIPAA, NYDFS e outros.
Try for free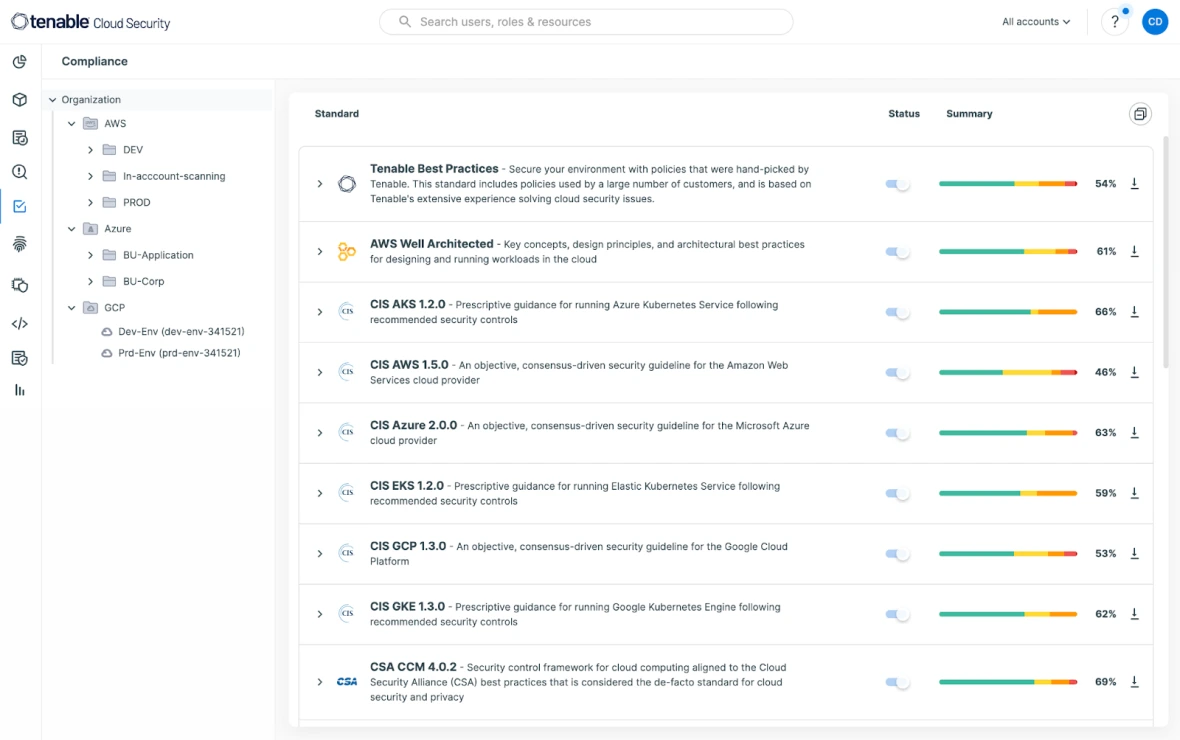
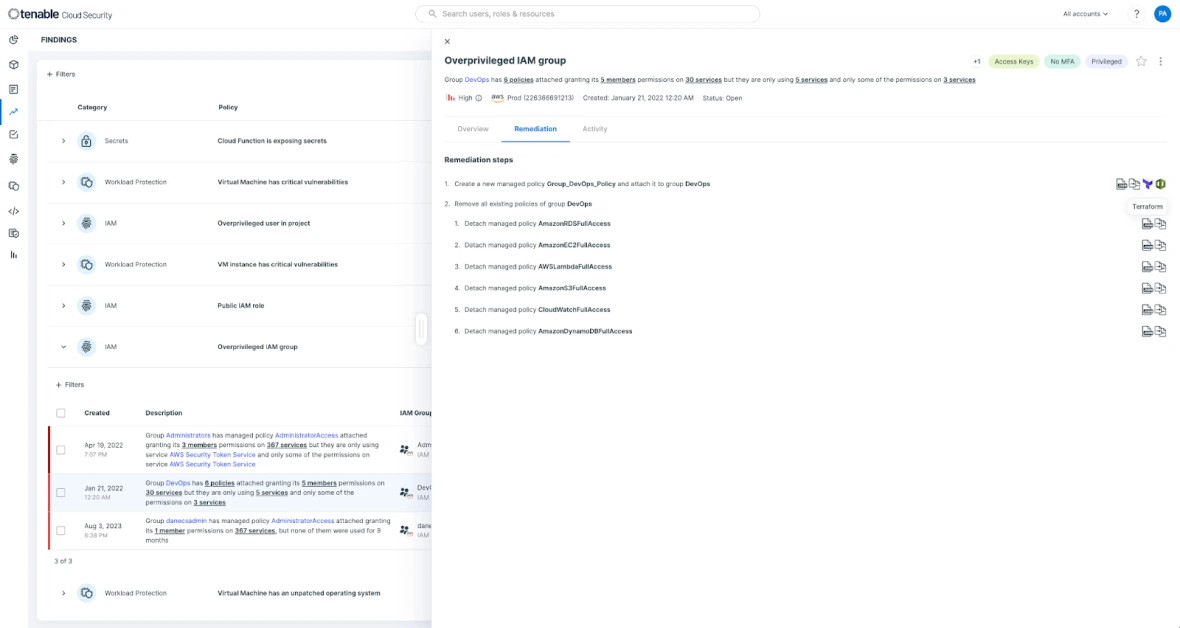
Tenable is a cloud security solution that allows you to focus on the risks that matter most. Tenable Cloud Security gives users deeply prioritized findings that empower Security and DevSecOps teams to automate threat detection and remediation efforts at scale. Mitigate and remediate risky privileges and faulty configurations using auto-generated and customizable policies by seamlessly integrating across ticketing, CI/CD pipelines, IaC, and other workflows.
Try for free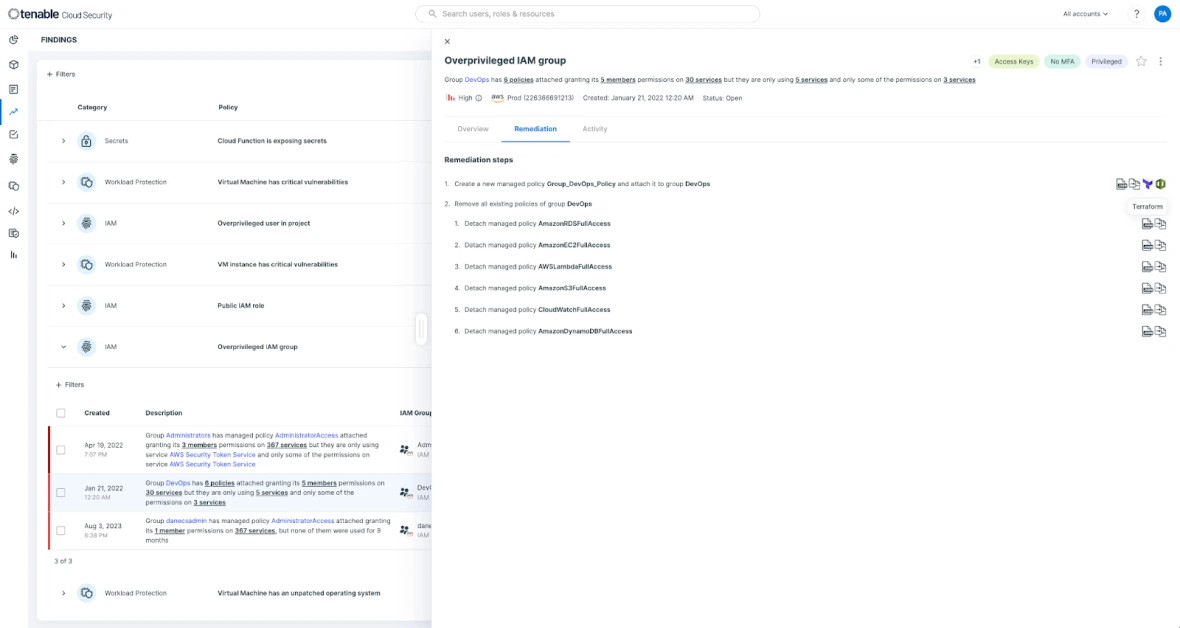
Reconheça atividades anormais e suspeitas avaliando continuamente o risco em relação às linhas de base comportamentais. Analyze cloud provider logs and link cloud threats with underlying architecture to show the context associated with each risk quickly.
Try for free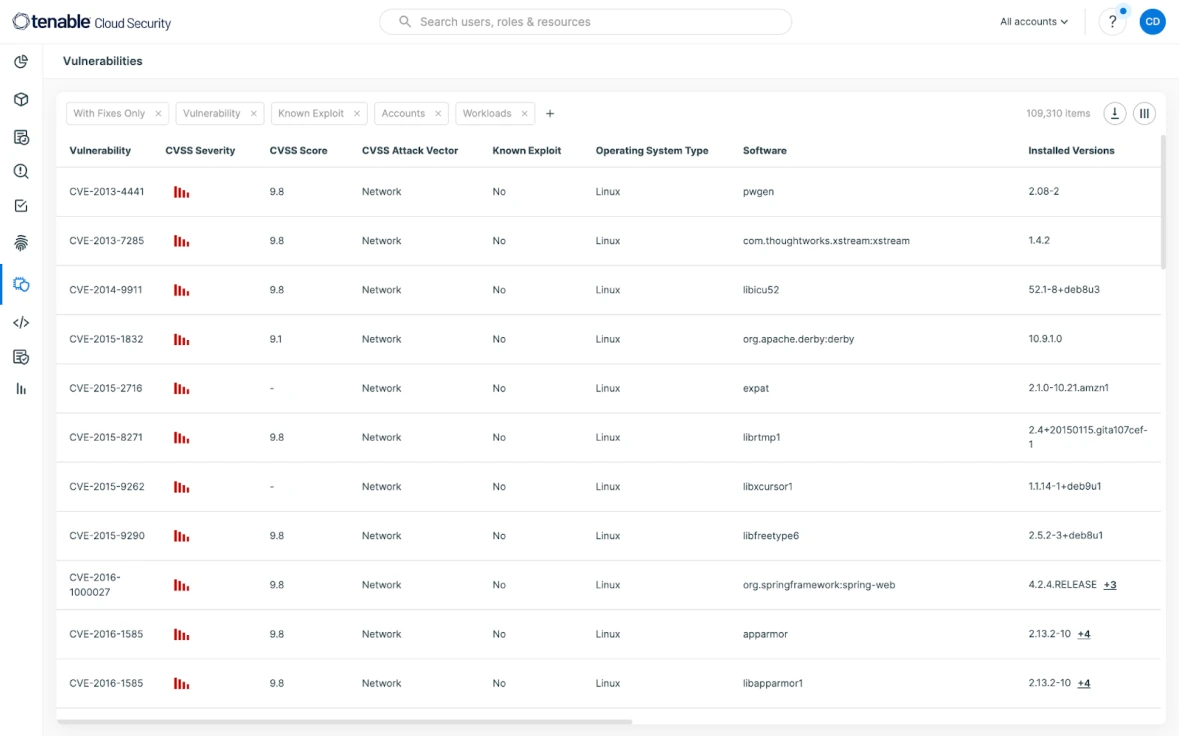
Build zero trust in your cloud security infrastructure. Minimize o excesso de permissões para serviços e pessoas, sem interromper nada. O caminho para o privilégio mínimo começa com uma imagem completa e precisa de todos os direitos. Continuously discover all entities and policies (including IAM, resource, permissions boundaries, and ACLs) in the environment and analyze the relationships to reveal the gap between desired enterprise policy and actual entitlements.
Try for free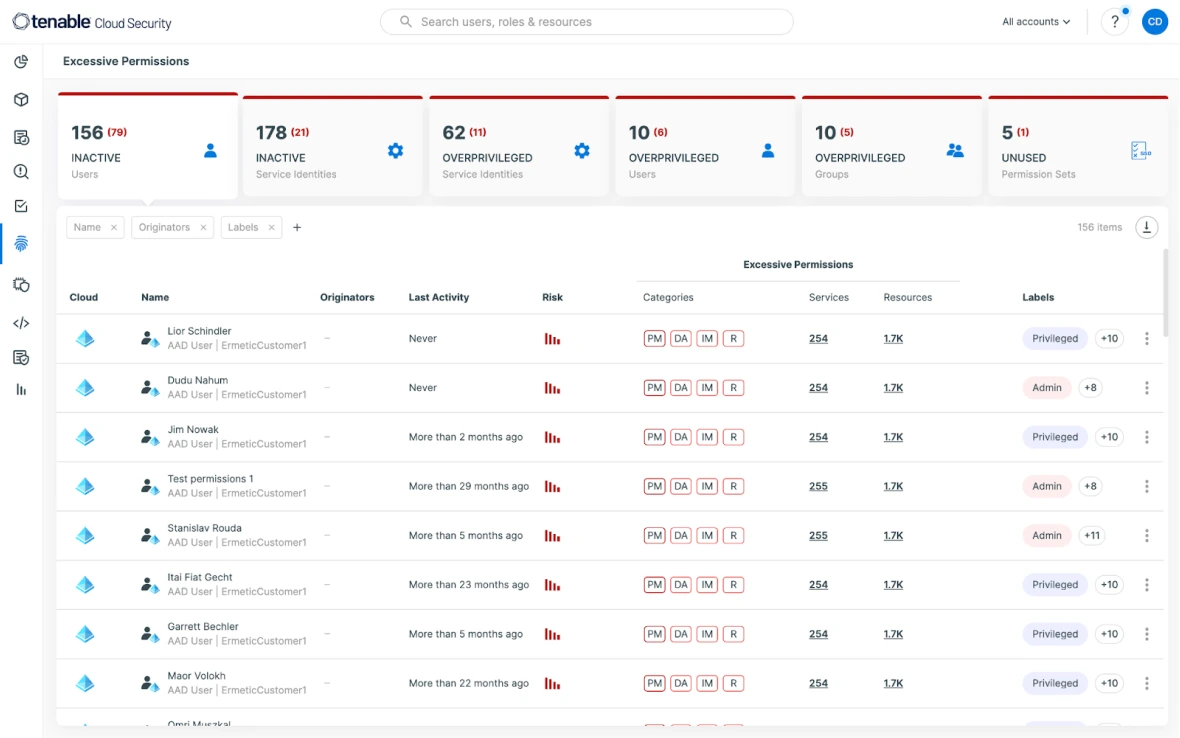




Leia o e-book para obter informações sobre:
- How to protect workloads and manage vulnerabilities
- Securing identities and entitlements and enforcing least privilege
- Ways to accelerate cloud detection and response
- How to assess and prioritize risk across cloud environments